Trust and Security on Data with Apture
Apture solutions ensure AI is used towards business and worker safety and productivity while protecting their privacy with high standard measures.
We collect and store
No Data
We don’t collect or store any data, whatsoever. Our models can be deployed on cloud or on premises by the business and the data that is sent for inference cannot be accessed by us. Nor will be the models trained on the user data without the user’s consent beforehand.
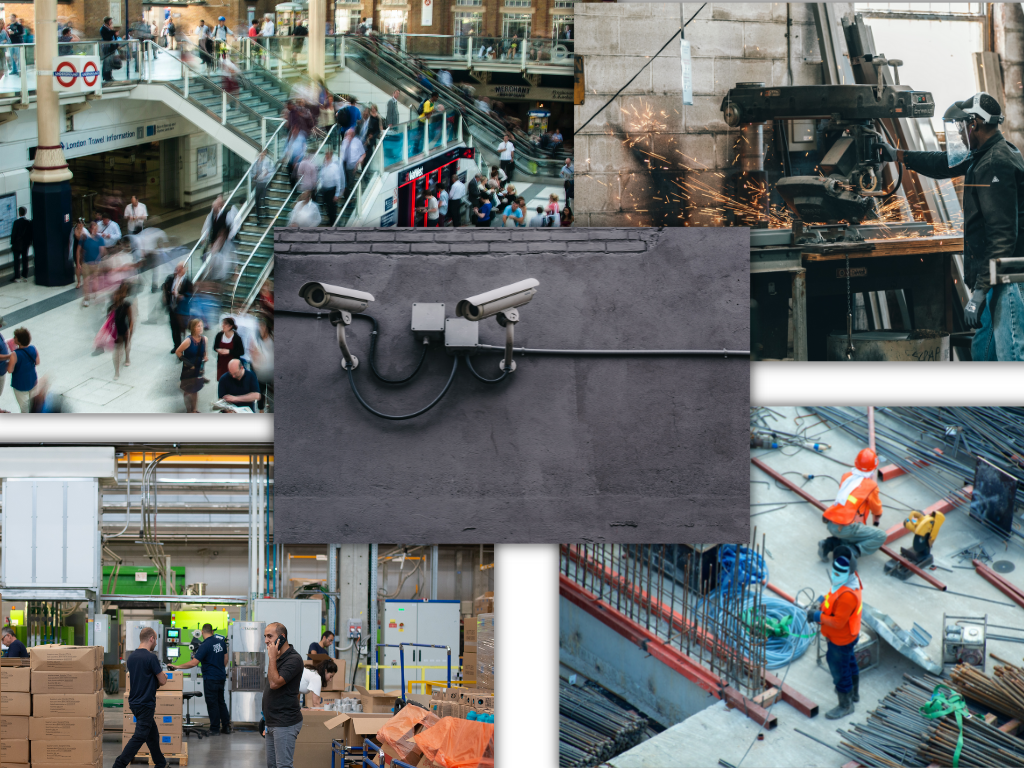
We are strictly focused on enhancing the possibilities of using computer vision in commercial settings and helping organizations grow with AI.
Practices we follow to protect user
privacy

Face Blurring
Data Encryption


User Authorization
"Cybercrime is the fastest-growing crime around the world and shows no sign of slowing down, estimating to cost the world an annual $10.5 trillion by 2025."
Choose an AI platform that keeps data privacy and security at the forefront.
Apture protects user privacy
in every way possible.
Security Compliance
Almost all security compliances are being followed while building and using Apture.
Flexible Deployment
Deployment options are very flexible and businesses can choose from what they like.
Edge AI offering
Using Edge AI technology models can be run on the edge keeping the data on premise.
Data Anonymization
The small amount of data that is processed is highly anonymized erasing all the privacy concerns.
Apture protects user privacy
in every way possible.

Deploy Computer Vision
With Safety and Assurity.
With Apture, it is possible to deploy CV in the most cost effective and productive way. We target multiple domains such as security, EHS, expressions and many more.
Be assured that with Apture, your data will not be compromised or used in any other way than what it was intended for.
What can you do to protect
privacy?
Frequently Asked Questions
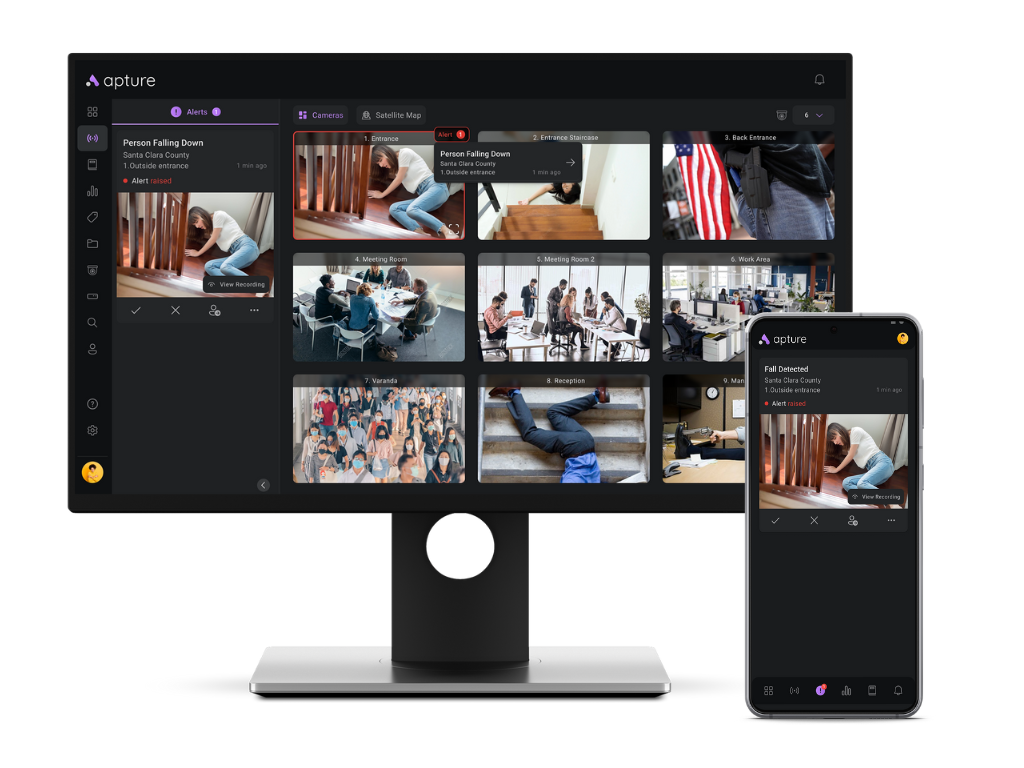
Our Context Aware Computer Vision Platform Product ecosystem is unique 'All-In-One' computer vision offering.
What differentiates us?
- An All-encompassing CV Platform Product Play
- Context based approach for CV solutions
- Pre-built Computer Vision solutions
- Frictionless personalized offering and experience